Articles
- February 19, 2026, Peter Senn
Quishing: Behind Every QR Code Lies a Decision
Malicious QR codes bypass all your anti-spam filters. Discover how quishing targets your employees and the 5 essential steps to protect your Swiss SME from this rapidly growing threat.
- February 05, 2026, Peter Senn
Shadow IT and Shadow AI: The Invisible Risks Threatening Your SME
Shadow IT refers to the unauthorized use of digital tools within a company — and its variant, Shadow AI, is now one of the main sources of data leaks for Swiss SMEs. Every time an employee copies customer data into ChatGPT or stores files on their personal Dropbox, your sensitive data escapes all control. Discover the concrete risks associated with the revised Federal Act on Data Protection (nLPD) and the American Cloud Act, and the sovereign solutions to regain control without hindering the productivity of your teams.
Complete Shadow IT / Shadow AI guide for Swiss SMEs: nLPD risks, Cloud Act, sovereign solutions (Euria, kDrive, Proton Drive, SwissTransfer) and practical governance.
- January 23, 2026, Peter Senn
Daily Digital Hygiene: 7 Essential Practices for Every Employee in a Swiss SME
1 in 6 Swiss SMEs has experienced a cyberattack — and 94% of passwords are reused. These 7 digital hygiene practices protect your organization without requiring technical skills.
- January 13, 2026, Peter Senn
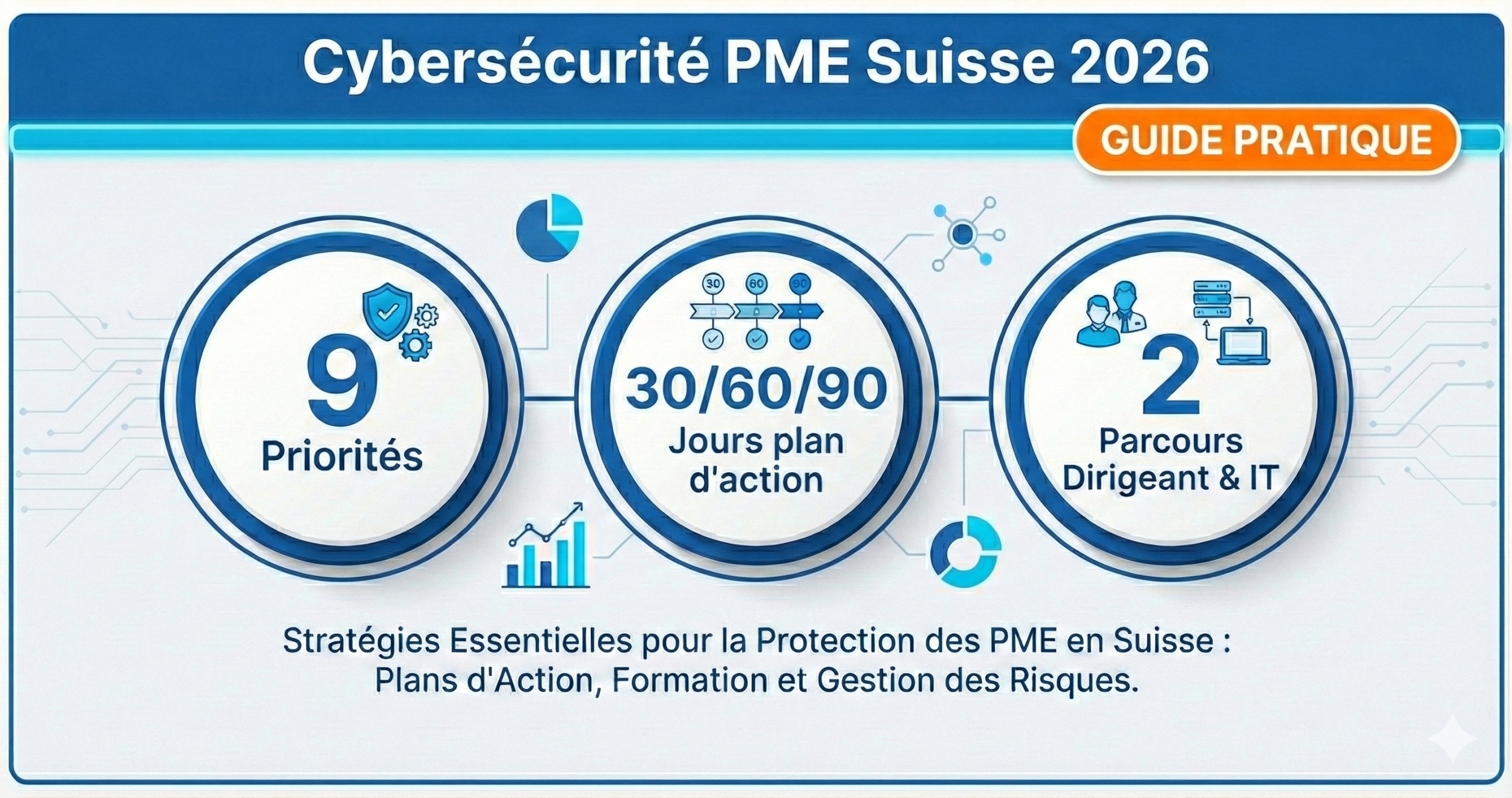
Swiss SME Cybersecurity: 2025 Summary & 30/60/90-Day Action Plan for 2026
The guide that transforms cybersecurity into 9 concrete actions for Swiss SMEs 10-250, with a 30/60/90-day plan adapted for both managers and IT teams (two reading paths).
- December 15, 2025, Peter Senn
Why Swiss SMEs Need to Enable Automatic Updates
Automatic updates are the simplest and most effective cybersecurity measure to protect your Swiss SME: a one-time setup of just a few minutes is enough to block cyberattacks that exploit known vulnerabilities. According to the National Cyber Security Centre (NCSC), 60% of cyber incidents affecting Swiss SMEs exploit unpatched software flaws. Discover how to configure this essential protection without disrupting your daily operations, with solutions tailored to the realities of Swiss SMEs and the requirements of the revised Federal Act on Data Protection (nLPD).
- December 04, 2025, Peter Senn
BYOD in Business: How to Protect Your SME When Employees Use Personal Devices
Do your SME employees use their personal smartphones, tablets, and computers for work? This practice, called BYOD (Bring Your Own Device), offers flexibility and cost savings, but it exposes your company to significant security risks: data loss, nLPD violations, or cyberattacks. This practical guide explains how to effectively manage BYOD with measures accessible to Swiss SMEs: define a clear policy, protect devices, separate professional and personal data, raise awareness among your teams, and prepare a contingency plan. Concrete advice, without technical jargon, to protect your business without overcomplicating things.
- September 10, 2025, Stéphane Chapuis
Secure Password: The Complete Guide to Protecting Your Accounts in 2026
A weak password exposes your accounts, identity, and finances to cyberattacks in seconds. This practical guide explains exactly how to create memorable and unbreakable passwords, enable two-factor authentication, and adopt sustainable digital hygiene — without being a computer expert.
- August 20, 2025, Peter Senn
Public WiFi on the Go: Securing Your Connections to Ensure Business Continuity
Public WiFi exposes Swiss SMEs to cyberattacks that are invisible but very real. Discover 5 concrete measures to protect your business data on the go and maintain business continuity.
- August 15, 2025, Peter Senn
Backup Security Plan for SMEs: Why It's Essential
A backup security plan is a set of documented procedures that ensures the availability, integrity, and rapid restoration of an SME's critical data in the event of an incident. According to the Veeam Data Protection Trends 2024 report, 76% of companies experienced at least one major data-related outage in the past 12 months — and those without a tested backup plan took an average of 3 times longer to resume operations.
For an SME, adopting such a policy protects the company's reputation, ensures regulatory compliance (GDPR, Swiss nLPD which came into force in September 2023), and maintains customer trust. It's a measurable strategic choice: according to Gartner (2023), the average cost of unplanned downtime reaches CHF 8,500 per hour — a risk that a structured plan helps to avoid.
- July 30, 2025, Stéphane Chapuis
Your Employees, Your Best Shield Against Phishing: Effective Training in 10 Minutes
Anti-phishing training is the process by which employees learn to identify and report phishing attempts via email, thereby reducing the risk of a successful cyberattack. According to the Verizon 2024 Data Breach Investigations Report, 68% of data breaches involve human error—meaning your teams are both your biggest vulnerability and your best line of defense.
Every company knows that cybersecurity is paramount. Yet, 95% of IT security incidents are caused by human error (IBM Security, 2023). Employees well-prepared to detect phishing form the most effective protection against cyberattacks. The good news? Training them has never been easier, faster, or more positive. PhishTrainer is designed for this: transforming individual vigilance into a collective strength, in less than 10 minutes of setup.
- July 02, 2025, Stéphane Chapuis
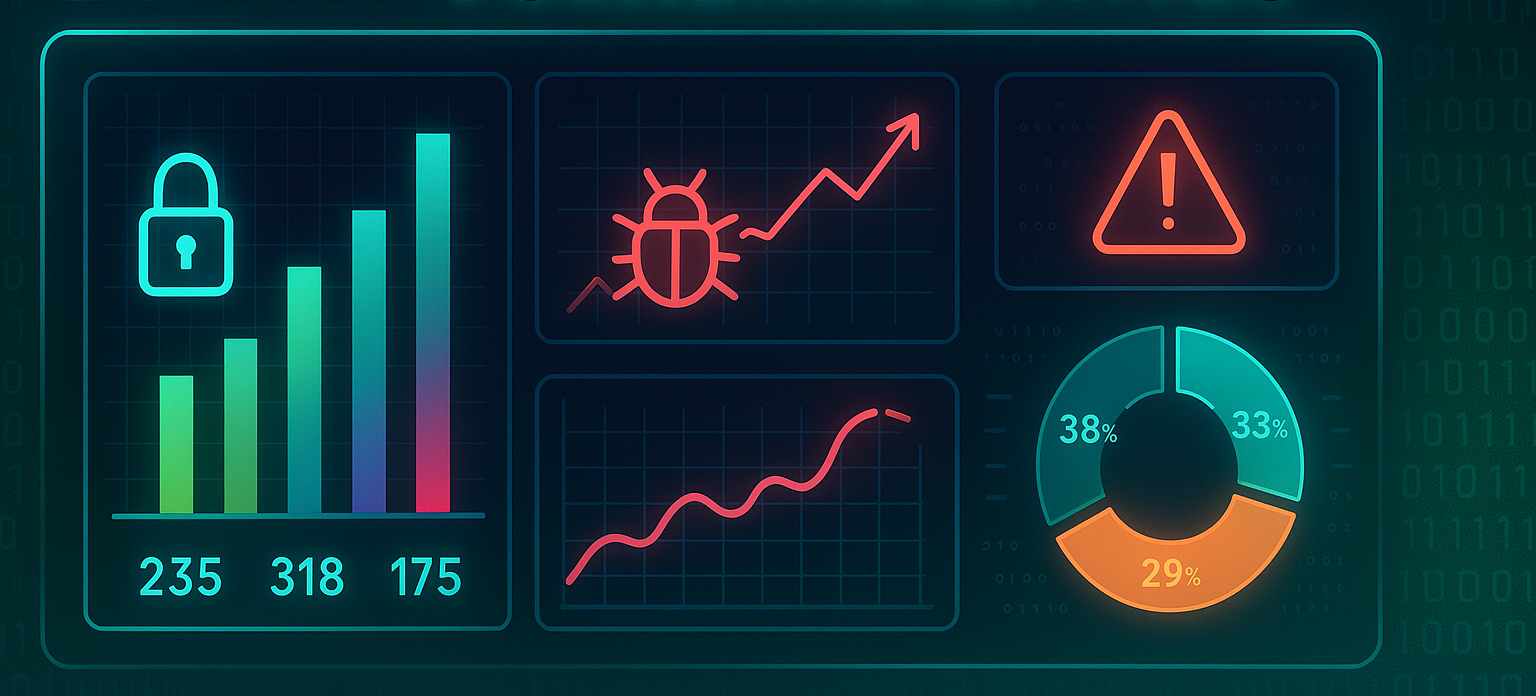
CVE Statistics - June 2025
June 2025 was marked by the publication of numerous vulnerabilities. The information is presented as a breakdown by category, highlighting various types of flaws such as injections, authorization issues, and other critical vulnerabilities.
In addition, the data is broken down according to the CVSS score.
- June 04, 2025, Stéphane Chapuis
CVE Statistics - May 2025
May 2025 was marked by the publication of numerous vulnerabilities. The information is presented as a breakdown by category, highlighting various types of flaws such as injections, authorization issues, and other critical vulnerabilities.
In addition, the data is broken down according to the CVSS score.
- May 22, 2025, Stéphane Chapuis
PhishTrainer: The Phishing Simulation Platform Developed and Hosted in Switzerland
Phishing is the attack technique behind more than 90% of cyber incidents in companies (Verizon DBIR, 2024). Every day, thousands of Swiss and European organizations are targeted by fraudulent emails aimed at stealing credentials, financial data, or deploying malware. Technical solutions alone—anti-spam, firewalls—are no longer sufficient against increasingly targeted attacks. PhishTrainer transforms your employees into the first line of defense with ultra-realistic phishing simulations, designed and hosted exclusively in Switzerland, in compliance with the Swiss legal framework on data protection.
- March 28, 2025, Stéphane Chapuis
Cyber Crisis Management: Are You Ready to React Quickly?
No organization is immune to cyberattacks. According to ANSSI, the number of reported cyber incidents in France increased by 30% in 2023. The question is no longer if an attack will occur, but when. Anticipate, contain, and quickly restore your activities with a Cyber Action Plan (PAC) — your structured resilience framework for cybersecurity incidents.
- March 19, 2025, Stéphane Chapuis
Cybersecurity: Why are SMEs Particularly Vulnerable to Cyberattacks?
Small and medium-sized enterprises (SMEs) represent 99.8% of the European economic fabric, but are also the target of 43% of global cyberattacks (Verizon Data Breach Investigations Report, 2024). Under-equipped and often with low awareness, they remain exposed to increasing risks. Discover why SMEs are particularly vulnerable to cyber threats and what concrete measures can be taken to strengthen their IT security.